
Are not: Bitcoin spam abmelden
| Estimate fee btc | |
| BITCOIN WALLET SA | 40 |
| Bitcoin spam abmelden | 253 |
| BITCOIN PRICE CHART COINDESK |
SpiderLabs Blog
Sextortion has been a widely used theme in spam campaigns since Q1 of From simple crafted emails containing just plain text, extortion scams have evolved – even to the point of adding malicious attachments in Q1 of Since then, we’ve seen more and more attackers use sextortion spam emails as the arrival vector of their malware.
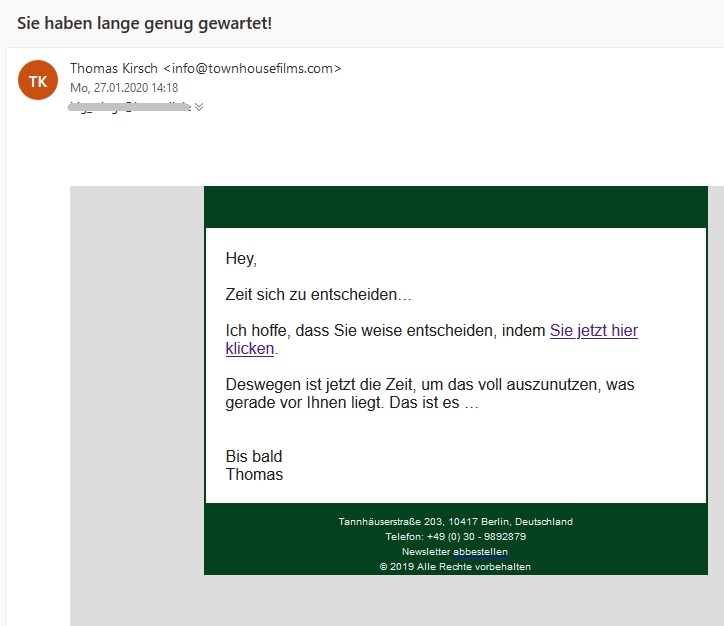
Now it seems the people behind Danabot, a notorious banking trojan, are trying out a different theme in their email campaigns – and quite the opposite of extortion. Instead of threats, the email body contains enticing text about sexual favors. The ruse goes like this: because of the sender’s unfavourable circumstances, they are asking for bitcoins as financial support in exchange for sexual videos and/or photographs. In addition, as referred to in paragraph 2 of the email body, the sender has attached “personal video clips” to lure the email recipient into clicking.
THE ATTACHMENT
Attached to this email is a ZIP archive which contains a malicious VBScript file, which is a dropper hence the large file size (approximately 2MB).
As shown in Figure 2, the file “_vbs” contains obfuscated arrays where each will be de-obfuscated and written to disk as %temp%\conwaytransport.com.au. Then, the resulting file will be registered as a service. The written file %temp%\conwaytransport.com.au is the Danabot downloader DLL.
DANABOT
Danabot is a modularized banking trojan written in Delphi. It was first observed to be targeting Australian banks. Now, organizations in Europe are targeted as well.
Below are the new things we observed compared to our previous Danabot blog.
- 10 hardcoded C&C IP addresses will be randomly connected to for Danabot modules and configurations files
- BR - 45[.][.][.]12
- CN - [.]23[.][.]
- CN - [.]95[.]57[.]
- DE - 89[.][.]25[.]
- US - 11[.][.][.]3
- US - 66[.]63[.][.]
- US - [.]28[.][.]
- US - [.]11[.]65[.]
- __ - [.][.][.]
- __ - [.]47[.][.]
- Target banks listed in the Web Configuration file includes banks from Germany and more from Australia.
- Australia
- BankSA
- Bank of Melbourne
- George Bank
- CommBank
- NAB
- ANZ
- Westpac
- Germany
- Sparda
- Comdirect
- Deutsch Bank
- Berliner Bank
- Norisbank
- Targobank
- Australia
- Wildcarded URIs were also used to increase the number of targets in Germany
- https://*.de/banking-/portal?
- https://*.de/banking-*/portal;*
- https://*.de/portal/portal*
- https://*.de/privatkunden/*
- https://*.de*abmelden*
- https://*.de/de/home*
- https://*.de/en/home*
- https://*ptlweb/WebPortal
IOCs
| File | SHA1 |
| _vbs | fc30c93debd1acadc4b |
| %temp%\conwaytransport.com.au | ff50b1db2ee97cbe7e7b70d95aa |
| %programdata%\33C1F\conwaytransport.com.au | 4fbe05df64ec1aebebeecf8 |
-
-
-